Cybersecurity Services.
Protect every organisation from all angles with expert end-to-end cybersecurity services. Work with experienced cybersecurity specialists following leading security frameworks to safeguard your business from the complex threat landscape.
Identify
Protect
Detect
Respond
Recover
Cybersecurity Services Built on Leading Frameworks.
Our cybersecurity services align with the globally recognised National Institute of Standards and Technology (NIST) Cybersecurity Framework. It is built on the core functions of Identify > Protect > Detect > Respond > Recover. The NIST Framework provides leading standards, best practices and guidelines to industry, government, and businesses to effectively understand, assess, manage, and prioritise cybersecurity risks.
Learn More About Our Approach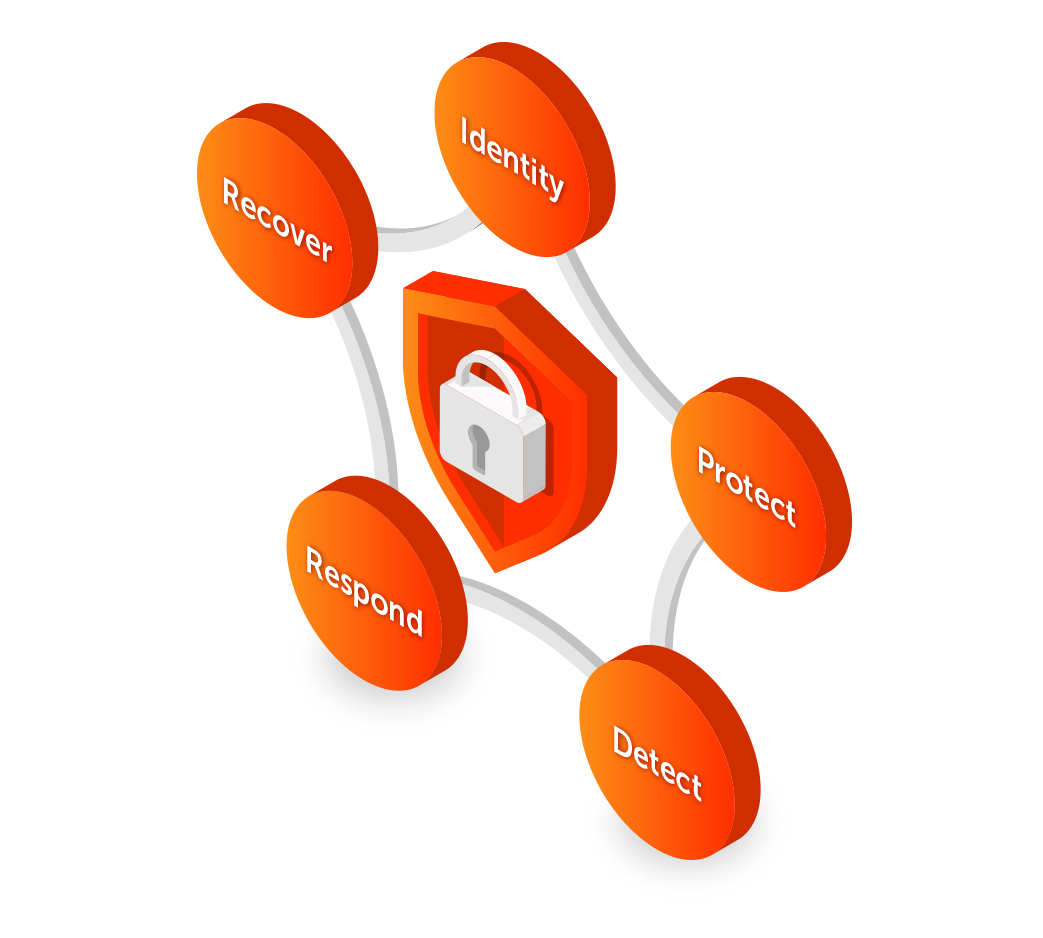
24/7 Security Operations.
As the threat landscape becomes more complex, real-time monitoring and incident response is more important than ever. We’re partnered with Arctic Wolf, the market leader in security operations, to offer a unique Security Operations Centre (SOC) service to proactively prevent, identify, and respond to cyberattacks 24 hours a day, 7 days a week.
Our partnership with Arctic Wolf provides an extension to our cybersecurity services portfolio to help our clients defend their organisation against the latest cyber threats. Provided by the 848 Group and delivered by the industry’s original Concierge Security Team, our SOC services include:
- Managed Detection and Response (MDR)
- Managed Risk
- Managed Security Awareness
- Incident Response

Tackle your Complex Security Challenges.
Identify, prevent, and manage risks posed by people, processes, and technology.
Assess and test your security architecture to reveal vulnerabilities and threats, and remediate your security weaknesses.
Have peace of mind your business is secure with expert managed security services and 24×7 SOC solutions.
Strengthen your cybersecurity posture and protect your critical business assets.
Deploy fit-for-purpose security solutions and develop a strategy that evolves with you.
Identify evolving threats and understand an attacker’s perspective so you’re always one step ahead.
Your End-to-End Cybersecurity Partner.
848 has a dedicated Cybersecurity Practice with a diverse team of IT experts to secure your IT systems, applications, and cloud environments. Our team identify your IT security gaps and implement leading cybersecurity services, solutions, and controls that protect your business inside and out.
We’re Cyber Essentials Plus Certified and experienced in ISO 27001 processes, and our cyber specialists deliver expert cybersecurity services underpinned by leading security frameworks including NIST, CIS and IASME.
Taking a holistic approach, we assess and test your security architecture to reveal human, technology, and process risks, and build fit-for- purpose solutions to resolve them.
